Your tech stack has holes in it. So does mine. In fact, every system I’ve ever built or managed over my 20+ years in tech has had vulnerabilities, edge cases, and failure points. The real question isn’t how to eliminate these holes—it’s how to stop them from lining up and creating catastrophic failures.
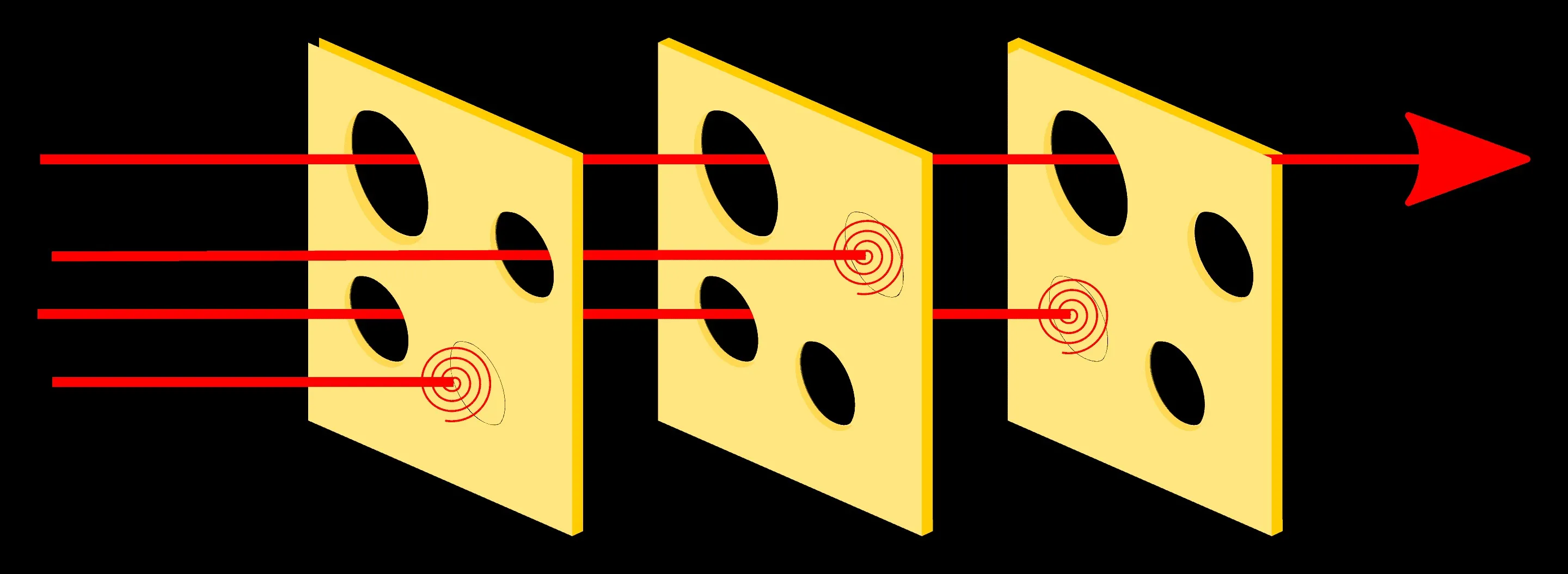
Back in 1991, a safety researcher named James Reason proposed a revolutionary way of thinking about system failures. He suggested that disasters rarely result from a single point of failure. Instead, they happen when multiple vulnerabilities in different layers of a system align—like holes in slices of Swiss cheese lining up to create a path through the entire stack.
A system fails when its vulnerabilities in multiple protective layers momentarily align, like holes lining up in slices of Swiss cheese.
Reason developed this model after studying catastrophic failures like the 1986 Challenger disaster, where it wasn’t just one component that failed, but a cascade of interconnected issues—from engineering decisions to management processes to communication breakdowns. The model transformed how industries think about safety and reliability, spreading from aerospace to healthcare and beyond.
While Reason originally created this framework for physical safety systems, I’ve found it incredibly powerful for understanding why things break in tech organizations—and more importantly, how to prevent disasters before they happen. In fact, I’d argue it’s more relevant than ever in our world of complex, interconnected systems.
The Stack of Swiss: More Than Just a Tasty Metaphor
Think of your tech infrastructure as a stack of Swiss cheese slices. Each slice represents a different layer of defense, for example:
- Your authentication system
- Input validation
- Error handling
- Monitoring
- Backup systems
- Security protocols
- Human processes
Each of these layers has holes—vulnerabilities, bugs, or failure points. The beauty of the model is that it acknowledges this reality: no single layer will ever be perfect. What matters is how we arrange these imperfect layers to create robust systems.
Learning From My Own Swiss Cheese Disaster
A couple of years ago, my team experienced a major data pipeline failure that perfectly illustrates this model in action. We had:
- A bug in our validation logic (hole #1)
- Monitoring that didn’t catch the invalid data (hole #2)
- A backup system that was temporarily disabled for maintenance (hole #3)
When these holes aligned, we had a complete system failure. The incident taught us that having multiple layers of defense isn’t enough—we need to actively manage how these layers interact.
Beyond Infrastructure: The Human Layer
Here’s where it gets interesting: the Swiss Cheese Model isn’t just about technical systems. Some of the most critical “slices” in your stack are human processes:
- Code review practices
- Deployment procedures
- Incident response protocols
- Team communication patterns
I’ve seen teams with beautiful technical architectures fail because their human layers were full of holes. A rigorous CI/CD pipeline won’t save you if your team has poor communication habits or unclear escalation procedures.
Making Your Cheese Work for You
So how do we apply this in practice? Here’s my approach:
- Map Your Cheese Layers
- Document every defensive layer in your system
- Identify known holes in each layer
- Look for patterns where holes might align
- Diversify Your Defenses
- Don’t rely on similar types of checks at different layers
- Mix automated and human verification
- Implement different types of monitoring at different levels
- Monitor Layer Health
- Regularly audit each defensive layer
- Track near-misses where holes almost aligned
- Maintain and update each layer independently
- Build Dynamic Defense
- Create systems that adapt when holes are detected
- Implement automated responses to potential alignments
- Foster a culture of proactive hole-patching
The Counterintuitive Truth
Here’s the part that took me years to accept:
💡
Trying to eliminate all holes is not only impossible—it’s counterproductive.
The goal isn’t to have perfect layers; it’s to have complementary layers whose strengths compensate for each other’s weaknesses.
Some of the most reliable systems I’ve built weren’t the ones with the fewest holes, but the ones with the best-arranged holes. They were designed to fail gracefully, detect issues early, and prevent cascading failures.
Post-Mortems: Your Swiss Cheese Detective Tool
Post-mortems are where the Swiss Cheese Model really shines. When analyzing an incident, most teams focus on finding “the root cause” — but this model teaches us that significant failures rarely have a single cause. Instead, use your post-mortems to:
- Map the Failure Path
- Identify every defensive layer that was breached
- Document how each layer failed to catch the issue
- Understand how these failures interacted
- Look for “Pattern Holes”
- Are certain types of issues consistently slipping through multiple layers?
- Do some layers tend to fail simultaneously under specific conditions?
- Which combinations of holes appear most frequently?
- Examine Layer Interactions
- How did communication flow (or not flow) between teams?
- Were there handoff points where context was lost?
- Did automation hide important signals from human operators?
The key is to transform your post-mortems from blame-finding exercises into systematic analyses of your defensive layers. Each incident is an opportunity to understand not just what went wrong, but how your protective measures interact.
I’ve started asking these questions in every post-mortem:
- Which layers of defense were involved?
- How did each layer respond?
- What information was available at each layer?
- How could we have detected this earlier?
- What prevented existing safeguards from catching this?
This approach has revealed patterns we never noticed before. Often, what looks like a monitoring failure also involves gaps in our deployment processes, communication protocols, and system architecture.
Making It Real: Action Items for Tomorrow
Start with these concrete steps:
- Map your current defensive layers
- Identify your critical holes
- Look for potential alignments
- Plan your next layer of defense
Remember: your goal isn’t to build a perfect system. It’s to build a system that’s resilient even when imperfect. That’s the true power of the Swiss Cheese Model in tech.
The next time someone on your team points out a hole in your system, thank them. They’re not highlighting a failure—they’re helping you prevent the next system failure.